Secure360 2022
· @jabenninghoffA couple of weeks ago, I spoke at Secure360 2022! My talk, “What Safety Science taught me about Information Risk” was an updated version of my SIRAcon 2021 talk (available in the members area at https://www.societyinforisk.org).
Session Description
Two years of study and research has changed how I see risk. Safety science taught me that improving performance is the key to managing risk, and studying successes is the key to risk analysis. The ‘New School’ of safety argues that you can’t have a science of non-events; safety comes through being successful more often, not failing less. Research in DevOps, Software Security, and Security Programs show a strong link between general and security performance. In many (but not all) cases, organizations most effectively reduce cybersecurity risk by improving general performance, not by improving one-dimensional security or reliability performance.
This talk presents a new model for security performance that informs how we can maximize the value of our security investments, by focusing on improving existing or creating new organizational capabilities in response to new and emerging threats, where general performance falls short. It will review both the theory that improving performance improves safety, how that relates to cybersecurity risk, evidence from my own and others’ research that supports this theory, and how it can be used to analyze and manage risk more effectively.
Talk
The talk is broken down into three sections, and covers both the theory as well as how to apply the theory to best improve security performance.
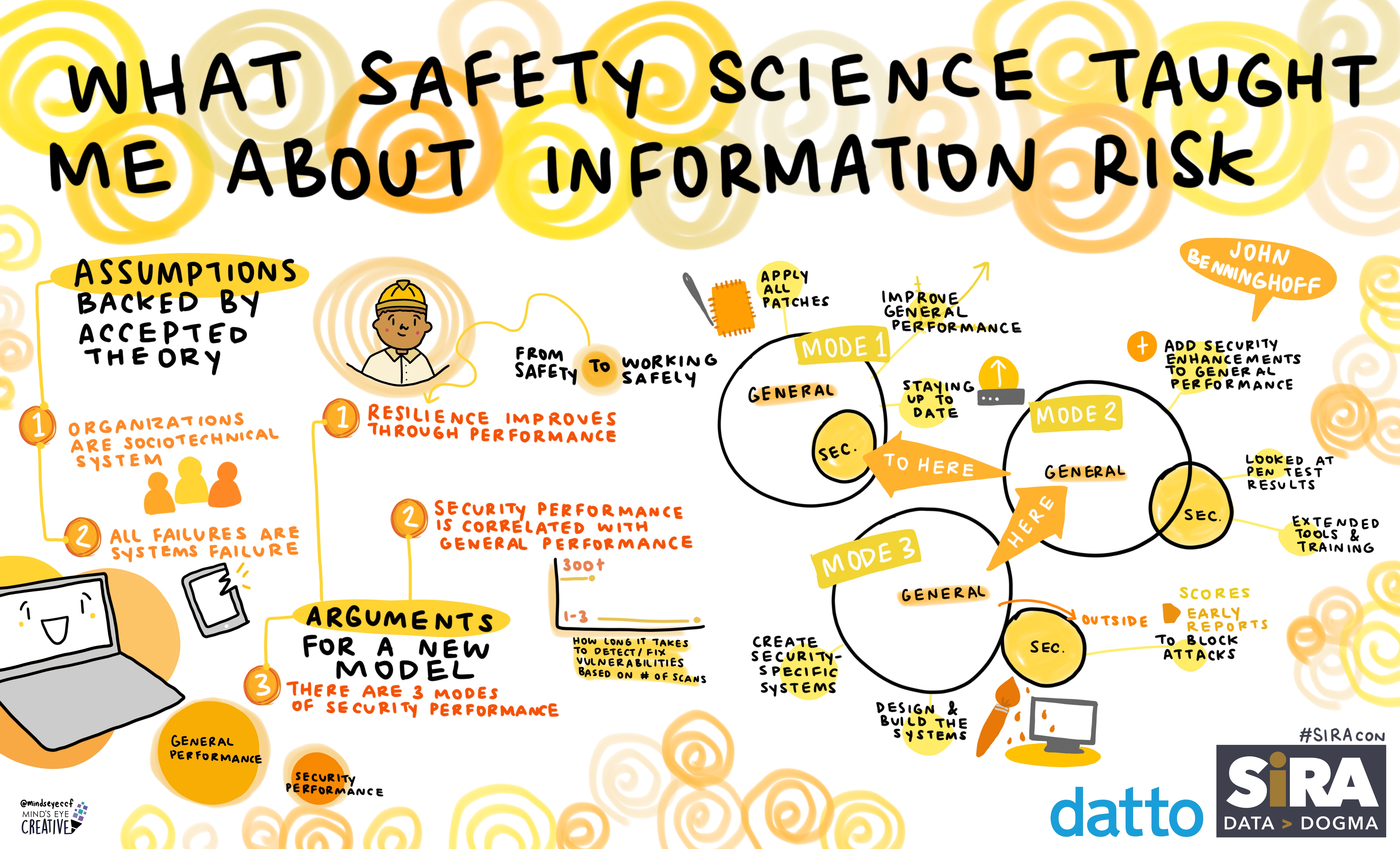
- Assumptions backed by accepted theory
- Assumption 1: organizations are sociotechnical systems
- Assumption 2: all failures are systems failures
- Arguments for a new theoretical model backed by evidence
- Argument 1: resilience improves through performance
- Argument 2: security performance is correlated with general performance
- Implications of the model for information risk management: optimize risk management based on your performance mode
- Mode 1: improve general performance
- Mode 2: add security enhancements to general performance
- Mode 3: create security-specific systems
- Guided Adaptability
- Work against the adversary
Overall, I think the talk went better than I expected. While the theory supports some potentially controversial conclusions, like “retire your vulnerability management program”, I had good engagement from the audience, ran out of time for questions and spent some time afterwards talking with a few attendees in the hall.
I got the survey results back pretty quickly. Only 9 people responded, which was maybe 10-20% (I’m not a good judge of crowd size), but those responses were very positive, with ~90% of attendees saying they would attend my future talks. My weakest score was, “I am Interested in hearing more of this topic” which scored just below “agree”.
Slides
My slides with notes, including references, are here.
Slides from all presenters at Secure360 (who provided them) are available here, and most of my past talks and security blog posts are available at https://transvasive.com.
Other Versions
I presented this talk two other times:
- As mentioned above, the original version was presented at SIRAcon 2021, those slides are available here.
- I was also selected to be a keynote speaker at my internal company technical conference in 2022! This was a condensed, 30-minute version of the talk, and draft slides from that talk can be found here.
Thanks to a generous sponsor, an artist created visual notes for my SIRAcon presentation! As a cool bonus, I have a laminated plaque with the visual in my office.